Enterprise-Grade Security Architecture in Salesforce
Introduction
As organizations scale digital operations, Salesforce serves as the central platform for customer data, revenue operations, service management, and analytics. Enterprise deployments increasingly involve multiple clouds, external integrations, mobile access, and distributed teams. While this enables agility and innovation, it significantly expands the security surface across identity, data, APIs, and infrastructure.
Weak access controls, misconfigured permissions, insufficient data protection, and lack of monitoring create material enterprise risks. Unauthorized access, data leakage, insider threats, and insecure integrations can lead to large-scale data exposure and regulatory violations.
This business case defines a comprehensive enterprise-grade security architecture for Salesforce focused on identity and access management, data protection, API security, network controls, and continuous monitoring to enable secure scalability with compliance alignment.
Business Problem
Enterprise Salesforce environments often evolve without centralized security governance. Multiple teams configure users, integrations, and permissions independently, resulting in inconsistent access policies and fragmented visibility into system activity.
Excessive user privileges are a primary risk. Over-permissioned profiles and roles allow users or compromised accounts to access sensitive records beyond their business need. Lack of periodic access reviews further increases exposure.
Data security gaps also pose a significant challenge. Sensitive information stored in Salesforce may not be properly encrypted, classified, or restricted at the field level, increasing the risk of data leakage or unauthorized sharing.
Integration security is another critical concern. APIs and connected applications often operate with broad permissions and weak authentication controls. Compromised credentials or tokens can expose large datasets.
Additionally, limited monitoring and auditing capabilities prevent organizations from detecting anomalous behavior in real time. Without centralized logging and alerting, security incidents may go unnoticed.
Regulatory frameworks such as GDPR, HIPAA, PCI-DSS, and SOC 2 require strict data protection, auditability, and access control. Poor security architecture directly undermines compliance obligations.
Proposed Enterprise Security Architecture
A layered security model is required to protect Salesforce environments at enterprise scale.
First, implement strong identity and access management. Enforce multi-factor authentication across all users, integrate with enterprise identity providers using single sign-on, and apply least-privilege access using profiles, permission sets, and role hierarchy.
Second, secure data across its lifecycle. Enable encryption at rest using platform encryption, enforce TLS for data in transit, and implement object-level, field-level, and record-level security controls to restrict access to sensitive data.
Third, strengthen API and integration security. Use OAuth 2.0 and JWT-based authentication for secure integrations, avoid password-based access, and enforce strict scope control. Store credentials securely and rotate tokens periodically.
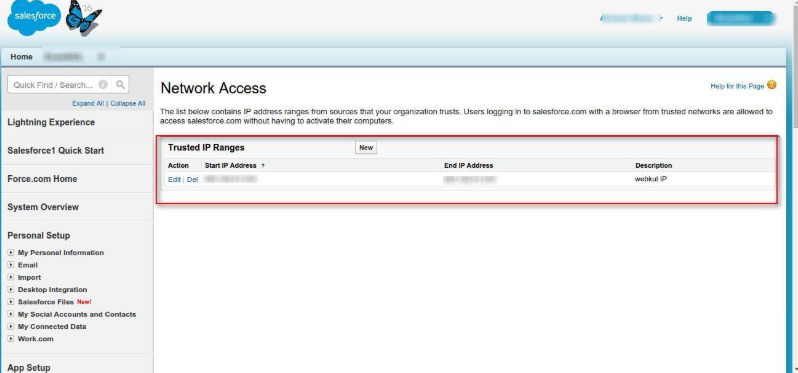
Fourth, implement network and infrastructure controls. Restrict access using trusted IP ranges, apply secure connectivity for integrations, and use web application firewalls to filter malicious traffic.
Fifth, enable continuous monitoring and auditing. Capture login activity, API usage, and data access events. Integrate logs into a centralized monitoring system to detect anomalies and trigger alerts.
Finally, establish governance and security operations. Conduct periodic access reviews, enforce security policies across environments, and define incident response procedures to handle security events effectively.
Identity and Access Control Configuration
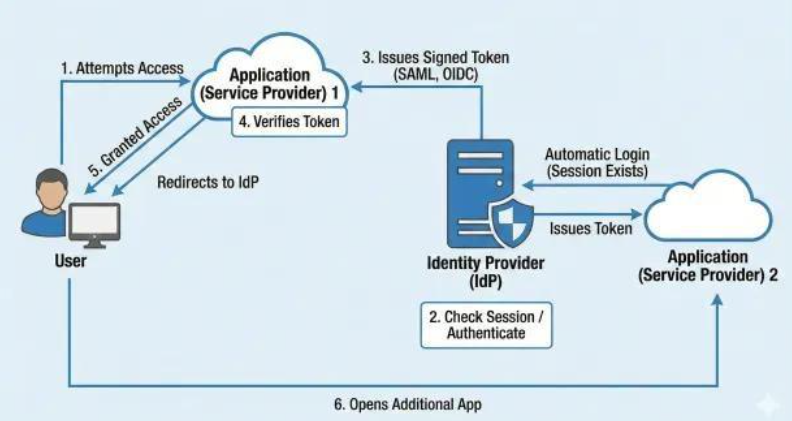
This section demonstrates how identity and access are configured in Salesforce using profiles, permission sets, and role hierarchy. It highlights enforcement of multi-factor authentication, integration with single sign-on providers, and implementation of least-privilege access.
Data Security and Encryption Controls
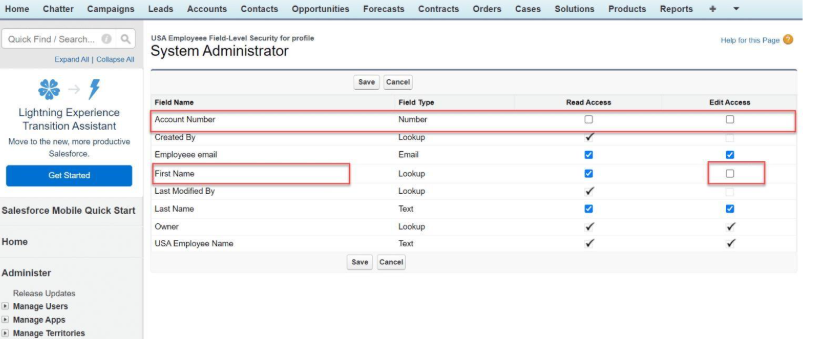
This section explains how Salesforce protects data using encryption at rest and in transit. It highlights field-level security, object permissions, and data classification.
API and Integration Security Architecture
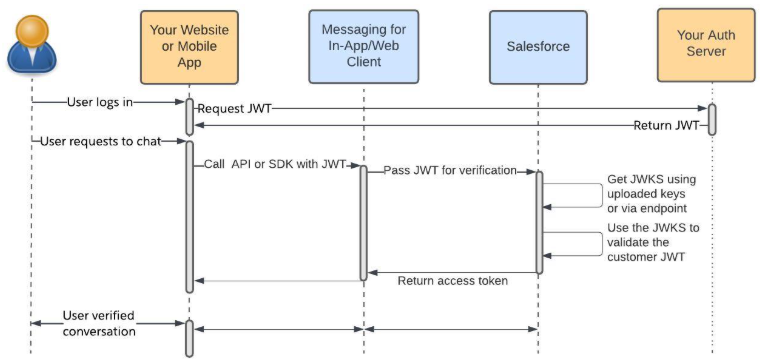
This section illustrates secure API integration patterns using OAuth 2.0 and JWT-based authentication. It emphasizes scope restriction, secure credential storage, and the use of dedicated integration users.
Monitoring, Logging, and Event Tracking
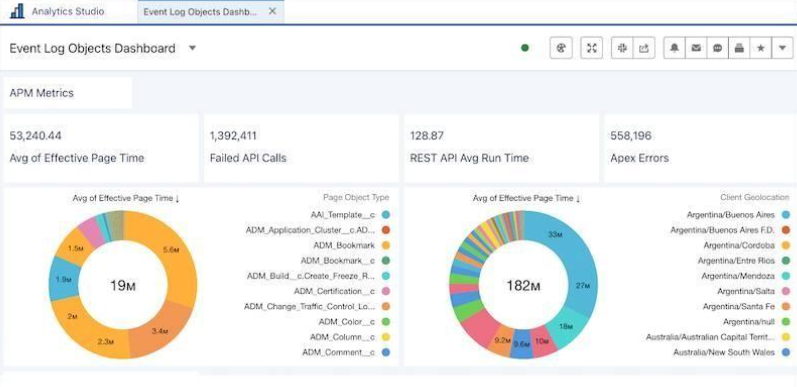
This section displays monitoring capabilities including login history, API usage tracking, and event logs. It demonstrates how organizations can detect anomalies and analyze user behavior.
Governance and Security Operations
This section explains governance processes such as access reviews, policy enforcement, and incident response.
Overall Theme
Security architecture should balance scalability with control. By implementing strong identity controls, robust data protection, secure APIs, continuous monitoring, and governance processes, organizations can build a resilient Salesforce environment.
Conclusion
A comprehensive enterprise-grade security architecture ensures that organizations can scale confidently while protecting sensitive data and meeting compliance requirements. Secure Salesforce environments are foundational to sustainable enterprise growth.


